In today’s interconnected online world, reliable technology is pivotal to most businesses who need their systems to operate seamlessly and efficiently.
With so many critical business services being technology dependnt, securing the systems which provide those services is now more vital than ever. The amount of confidential business data organizations produce and store on a daily basis, has grown exponentially, and this data is a valuable commodity. In today’s information economy, data is the new currency and organizations need to put measures in place to protect it.
Passwords Are No Longer an Adequate Defense
The username and password combination, which has been the principal login mechanism for secure access for decades, is no longer an adequate defense against today’s determined attackers. Data breaches are a daily occurrence, and weak or stolen passwords are responsible for over 81% of these system compromises.
The fact is people are the weakest link in the security chain. They reuse the same password on multiple systems or choose passwords which are easy to guess. Attackers leverage these poor password practices and utilize techniques like credential stuffing, which involves the use of previously stolen credentials, or password spraying, that exploits lists of commonly used passwords, to automate attacks against systems.
Protecting an entire system or organization with a string of characters is no longer a sufficient form of protection in today’s digital world. It only takes one weak credential to compromise an entire system and organizations need to implement measures which eliminate this material risk.
What is Two-Factor Authentication?
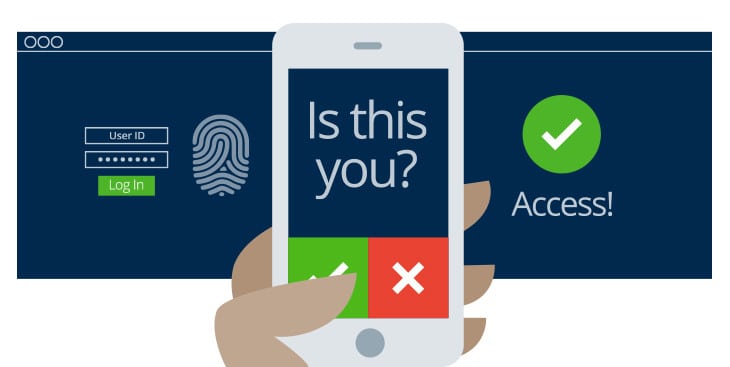
Two-Factor Authentication (2FA) is a multi-layered, defense in depth approach to security and involves a user submitting a second factor during the login process. By requiring a second authentication factor, systems can mitigate the inherent risks which exist in single password authentication systems.
2FA is not a new technology paradigm. Requiring two factors to authenticate has been part of the banking industry for years where both an ATM card and a PIN are needed to access financial accounts. As organizations have become more digital, the need to protect business data with the same level of resilience has led to the creation of innovative 2FA solutions which provide the secure authentication needed in today’s online world.
Which Secondary Factors Provide the Best Security?
There are a variety of secondary factors which organizations can use to improve their authentication security. These range from simple solutions such as asking a security question during the authentication process, to advanced technical implementations of biometric-enabled login devices. These secondary authentication factors fall into three primary categories: something you know, something you have, and something you are, and each one has a different level of assurance associated with it.
Knowledge Factors – Something You Know
Passwords, PINs, and security questions are second-factor authentication mechanisms which fall under the category of something you know. Because these factors rely on the human element, they rank quite low on the assurance scale. As stated previously, people reuse these factors on multiple systems or choose to use one which is easy to guess. For example, account resets often use security questions which ask the user to submit information which is easily obtainable with a quick social media search, such as their mother’s maiden name. When choosing PINs, people often select their date of birth or something similar which is easy for them to remember, and simple for someone else to guess.
Possession Factors – Something You Have
Using possession factors as a second-factor authentication mechanism is more secure than using a knowledge factor such as a password or PIN. The mere fact that a user needs to have an item in their possession during the login process adds a layer of security which is difficult to compromise.
There are a variety of possession factor solutions which organizations can utilize for this purpose. The smart card is a good example and has been in use for some time as mentioned in our banking analogy. Other possession factor solutions include the use of a mobile phone where 2FA systems can send a One Time Pin (OTP) via SMS or voice, or where dedicated authentication apps loaded on a smartphone provide a rotating number sequence which is valid for a short period. Dedicated 2FA devices are also available which users can plug into their computer via a USB port. Physical tokens are another popular 2FA possession factor solution which involves a device displaying a random number sequence which rotates periodically.
Personal Factors – Something You Are
The secondary authentication factors which fall under the category of something you are, generally consist of biometric solutions. Here systems use fingerprint, palm or iris scanners, facial recognition, and even personal traits like an individual’s gait, to provide the second factor needed for secure authentication. Because these factors are fundamentally unique to an individual, they rank high on the assurance scale and protect against password attacks, but they are not foolproof. Biometrics are in the public domain. People leave their fingerprints everywhere, and their faces are in photographs across a variety of social media platforms. Furthermore, reissuing a compromised biometric factor is not possible. You can reset a password if it is lost or stolen, but you cannot reset a fingerprint. Even with these weaknesses, biometrics offer the necessary protection needed against automated password attacks.
2FA as a Service
Implementing a 2FA solution can be a complicated process especially if organizations need to retrofit their existing authentication systems. As commercial cloud services have matured in recent years, several solution providers such as Duo have emerged which provide this functionality as part of an Identity as a Service (IDaaS) platform. These cloud-based identity providers, not only enable organizations to consume 2FA as a service, but offer a full range of identity and access management solutions which include user and device lifecycle management, seamless integration into a variety of apps, and visibility into an organization’s identity landscape with proactive alerting and reporting.
The Easier Way to Implement 2FA
In today’s digital economy where organizations rely on their systems and customers expect businesses to keep their confidential information safe, single password authentication systems are no longer a sufficient form of protection. Organizations need to implement 2FA solutions to shield systems from data breaches and the detrimental effects they can have on their business.
Selecting an appropriate secondary factor which is easy to implement and aligns with business requirements can be a complex undertaking. Instead of trying to implement 2FA in isolation, organizations can consume these services from a cloud-based identity provider. By choosing to implement 2FA via a specialized third-party, organizations gain not only the benefits of a 2FA solution but also the opportunity to enhance their security with a comprehensive identity and access management service.
Synditech provides professional consulting and managed IT services in Vancouver BC. If you are looking to implement two factor authentication or just want someone to assist you with your cyber-security road map, get in touch with our Synditech team today.